Hi everyone,
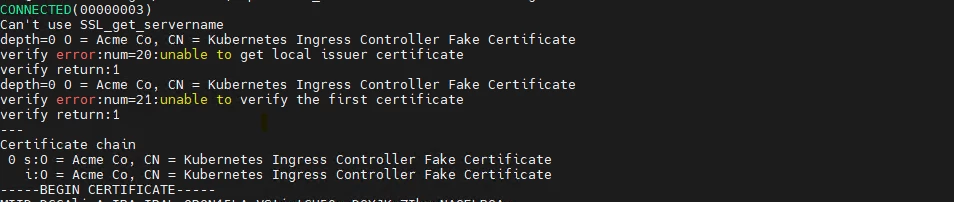
We are trying to call the IFS web service CustomerOrderService.svc from our Oracle APEX environment. The IFS URL is configured with a virtual host name, and we have downloaded the SSL certificate from the browser and imported it into the Oracle database wallet.
However, when we call the web service from APEX/Oracle DB, we receive the following error ORA-29024: Certificate validation failure.
Please advise if we are missing anything