Hello,
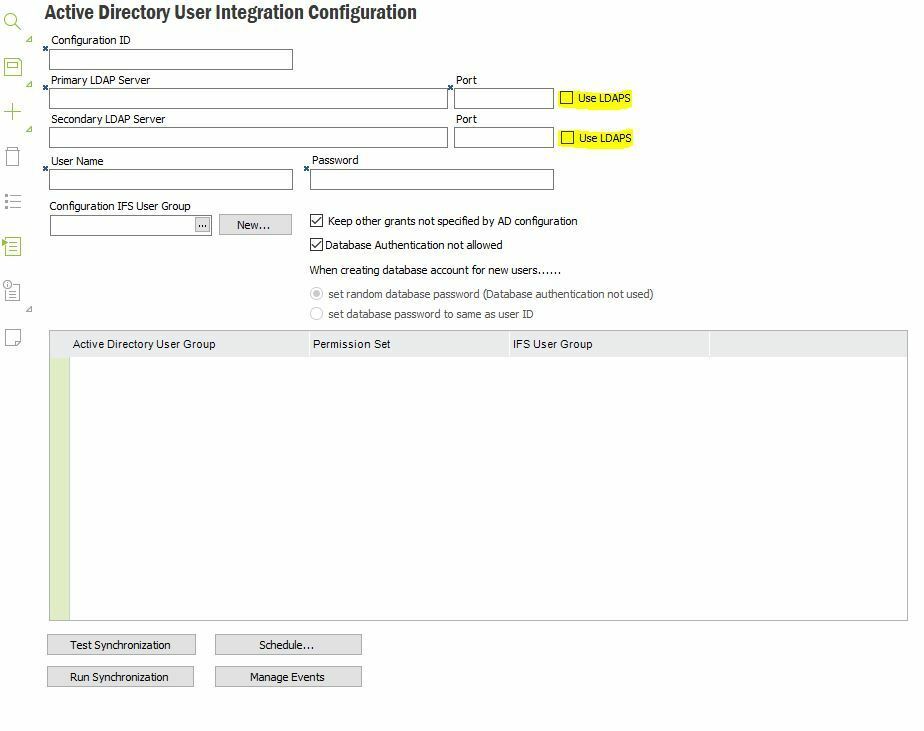
Customer is running on IFS Apps9 with SSO and Active directory synchronization.
Could you please advice, how we can ensure that Apps9 will work properly with LDAP channel binding and LDAP signing on Active Directory Domain Controllers?
The link on announced update from Microsoft:
https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/ADV190023
Best regards,
/Jozef