URGENT BULLETIN
IFS Advisory: IFS Products, Services and Log4j
IFS Advisory: IFS Products, Services and Log4j
Update (22nd December 2021 8:30 UTC)
Thank you to everyone who has actively participated in this KBA. We trust that the questions asked and the responses given have been of benefit to wider understanding of the mitigation of CVE-2021-44228 with respect to IFS products and services. Questions have however now started to move beyond this particular CVE and in to the area of customer-specific issues that are hard to track in a single threaded article, so this KBA is now closed to further comments. If you have product support issues please therefore report them through your usual support channel, or if you have questions or advice to share related to your experience with mitigating this vulnerability, please use the appropriate Community forum.
Update (21st December 2021 13:30 UTC)
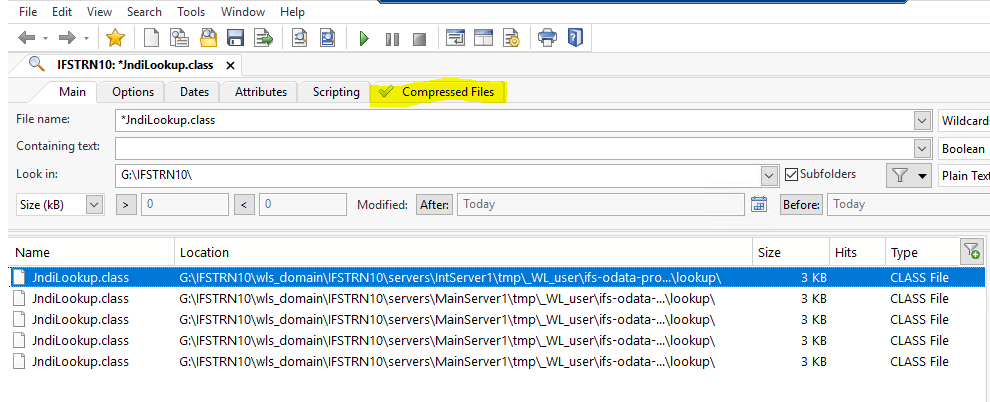
IFS Developer Studio update 21.82.845200.20211220 is now available. This update contains the fix (JndiLookup.class removal) that mitigates the log4j vulnerability CVE-2021-44228 when deploying to the local server on the developer machine. Please read the KBA article for information on how the tool is updated.
Update (20th December 2021 12:30 UTC)
IFS Cloud 21R1 SU9 is now available within the LE portal and completes the remediation deliveries for IFS Cloud with regard to CVE-2021-44228 vulnerability. This is also completes the delivery of all necessary remediations for all IFS products for this vulnerability. IFS on-premise customers are strongly recommended to apply the available remediations at the earliest opportunity. The impact KBA has been updated accordingly.
Update (19th December 2021 13:30 UTC)
IFS Cloud 21R2 SU2 is now available within the LE portal and remediates the CVE-2021-44228 vulnerability. IFS Cloud 21R1 SU9 is in the final stages of deployment and is planned to be available on 20th December 2021. The impact KBA has been updated accordingly.
Update (17th December 2021 17:15 UTC)
The impact KBA has been updated to reflect the availability of the IFS Maintenix Service Update. Information on this and further important updates regarding mitigation actions relating to the IFS Maintenix product are available here.
Update (17th December 2021 17:00 UTC)
The impact KBA has been updated to include guidance for IFS Applications 10 on-premise and remote environments.
Update (17th December 2021 14:30 UTC)
The impact KBA has been updated to include guidance regarding IFS development tools.
Update (17th December 2021 14:00hrs UTC)
Oracle has announced that Oracle Weblogic is affected by CVE-2021-44228. However, whilst Weblogic bundles Log4J, IFS is not enabling it nor including it in any CLASSPATH and therefore this is not an issue that needs mitigation. IFS will provide the relevant Oracle patches with the next Oracle CPU to fully remediate the issue.
For those with an Oracle Support account, further information can be found at the following locations:
- https://support.oracle.com/rs?type=doc&id=2827793.1
- https://support.oracle.com/epmos/faces/DocumentDisplay?_afrLoop=392129710573466&id=2827611.1&_afrWindowMode=0&_adf.ctrl-state=1832tvrio4_4
Update (16th December 2021 13:00 UTC)
The impact KBA has been updated.
Protection against CVE-2021-44228 for IFS Applications 10 on premise deployment is now in final test and anticipated for release 17th December 2021. This protection will also be included in IFS Applications 10 Update 15 planned for release on Thursday 3rd March 2022.
Update (16th December 2021 12:45 UTC)
Mitigation to protect against CVE-2021-44228 is now in place for IFS Applications 10 in the IFS Cloud Service. Full remediation for IFS Apps 10 Cloud Service customers is in test and further details regarding deployment will be posted in the bulletin.
Update (16th December 2021 9:00 UTC)
The impact KBA has been updated to reflect that all customer environments for IFS Cloud in the IFS Cloud Service now have mitigation applied. Mitigation for remote or on premise IFS Cloud customers and all IFS Applications 10 customers regardless of deployment type are in test. Service Updates for IFS Cloud and IFS Applications 10 are also in test.
Update (15th December 2021 19:30 UTC)
Our KBA has been updated to reflect that IFS Fleet Planner service updates are now fully applied.
Update (15th December 2021 16:00 UTC)
IFS are following closely the ongoing analysis regarding CVE-2021-45046 and would highlight that our remediation is currently based upon the Log4j 2.16.0 fix. Remediations already completed using 2.15.0 will be updated to 2.16.0 where applicable. We will continue to monitor further developments and keep our knowledge base article aligned accordingly.
Update (15th December 2021 15:30 UTC)
The IFS Cloud Service Updates 21R1 SU9 and 21R2 SU2, originally scheduled for release on Thursday 16th December 2021, will be available on the LE Portal by Sunday 19th December 2021 for you to apply to your environments and which will include the remediation patch for CVE-2021-44228. Changes for these updates are now complete and we are starting the test and deployment processes this evening. We will continue to update the KBA to reflect the status as these processes complete.
Update (15th December 2021 13:05 UTC)
The Impact KBA has been updated to reflect the fact that ESM assystIPaaS mitigation has been applied in the Cloud and mitigation is available for on-premise customers. Additionally, IFS Cloud customers in APAC now have mitigation applied and EMEA customers will be completed by midnight UTC today.
Update (14th December 2021 18:17 UTC)
The Impact KBA has been updated to confirm that Clevest is not impacted by the vulnerability
Update (14th December 2021 17:00hrs UTC)
IFS has made significant progress in understanding the impact of CVE-2021-44228, known colloquially as Log4j, upon our products and services. It is important to note that only a limited number of IFS products are affected and IFS is currently preparing a service update for those affected products. We have produced a knowledge based article available here which we will update regularly as our work continues. Understanding, mitigating and remediating this vulnerability is our absolute priority. Thank you for your patience while we complete this process.
Update (14th December 2021 07:45hrs UTC)
The situation surrounding this vulnerability and specific versions of log4j that are affected continues to evolve across the software industry. The current state is that log4j version 2.15 and above is unaffected but prior versions are potentially vulnerable to this exploit.
Whilst investigations continue please avoid using vulnerable versions of log4j in any customization or integration projects that may result in your IFS installation being compromised.
Update (14th December 2021 07:00hrs UTC)
For IFS Maintenix customers wanting to understand the impact of CVE-2021-44228, please see the detailed impact assessments and mitigation actions available in the following articles:
Update (13th December 2021 15:45hrs UTC)
The following IFS products are confirmed unaffected by CVE-2021-44228.
- Astea Alliance
- Astea FieldCentrix
- CE
- Customerville
- FSM
IFS continues to analyse the impact of this vulnerability on our remaining products and services and will update this bulletin as confirmed information becomes available.
13th December 2021 - 11:00hrs UTC
There have been widespread media reports regarding the open source Apache Software Foundation log4j Java logging component which was discovered to have a critical vulnerability CVE-2021-44228. Since its discovery, IFS has been analysing its impact upon our products and services and can confirm that this component is used within a number of our solutions.
Owing to the complex nature of the vulnerability and specifically the various environmental conditions that need to exist to make it exploitable, our analysis is still ongoing to establish what form mitigation and remediation might take.
Over the coming days we will continue to provide regular updates and mitigation/remediation information, both with respect to customers of the IFS Cloud Service and remote. Communication related to this vulnerability will continue to be posted to this IFS Community thread until further notice.
PLEASE ‘SUBSCRIBE’ TO THIS KBA TO RECEIVE NOTIFICATIONS OF UPDATES