We have a middleware service, that is serving 4 instances of IFS on a UAT basis.
All of these instances can be connected to using the URL https://ifsinstancename.microlise.com/”port”
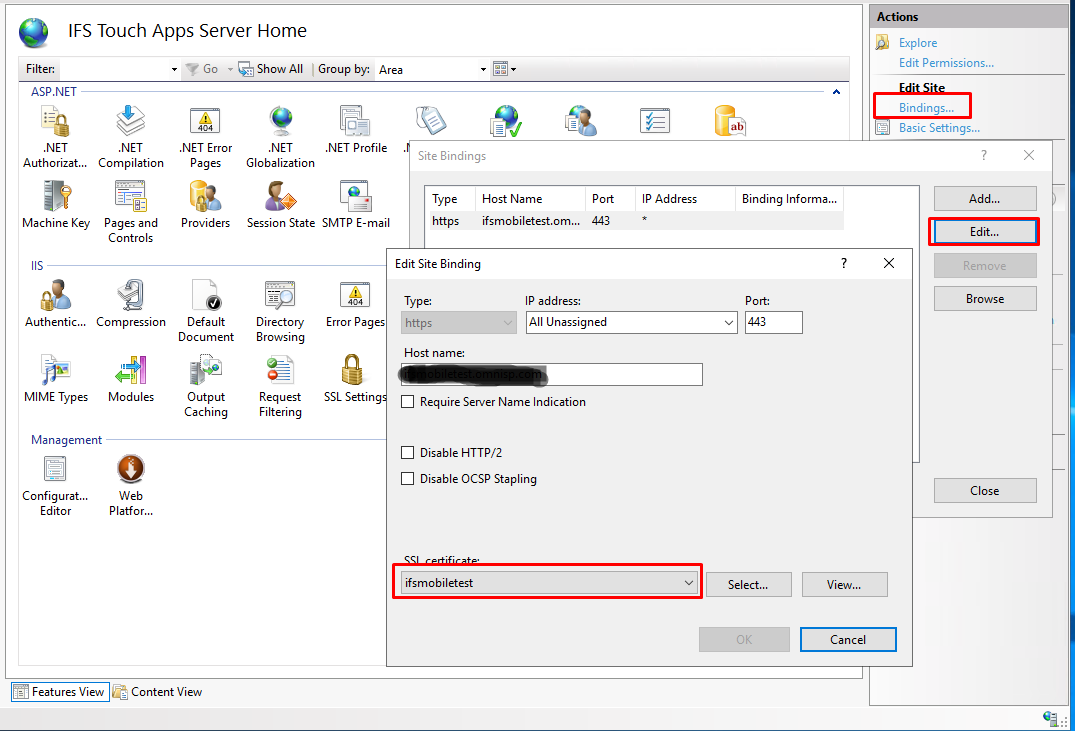
However, on the Windows IIS Manager, there isn’t a bindings section that covers the https connection.
I need to update a soon to expire digital certificate, but cannot find where it picks up the bindings for it.
Does anyone know how I can resolve this, or should I log it with IFS support?
Thank you for looking.
Kind regards
Richard.